How to Check Open Ports in Ubuntu
Learn various ways to check open ports in Ubuntu command line.
The open port is nothing but a port that is assigned to a specific application that is currently being utilized.
Of course, this was just one of many reasons why one should check for open ports before running an application.
For instance, you can use the ss command with -ltmp option to get open ports including processes:
sudo ss -ltunp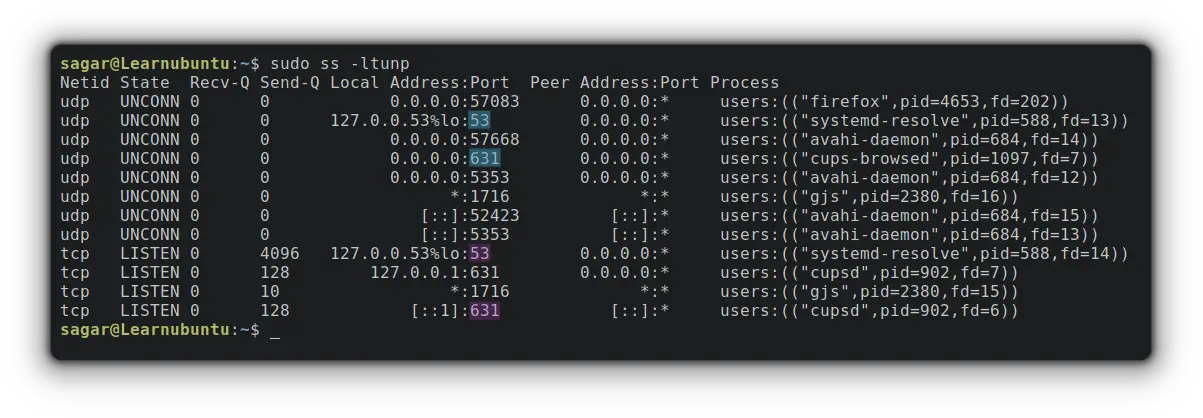
As you can see port no. 53 and 631, which are opened by default and used for DNS and the internet. You can thus make a decision whether these ports should be allowed through firewall or they have to be blocked.
Want to learn more about the widely used networking ports? The given guide would be helpful:
This was one way to list open ports. And you must be curious to know other methods, right? So let's kick off this guide with the first method.
1. Using nmap Command
The nmap (Network Mapper) tool is generally used by network engineers for OS detection, port scanning, network auditing, etc.
And unlike any other utility, nmap can get you open ports on remote machines without having access to them and does not require root privileges.
You need to install nmap on Ubuntu first:
sudo apt install nmapTo check open ports on localhost, you just have to pair nmap with the localhost option:
nmap localhost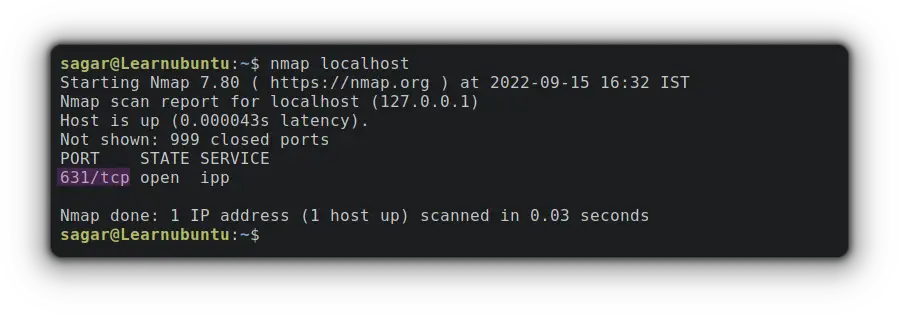
By default, nmap will get you TCP ports only. To list TCP and UDP ports at the same time, you'd need to use -sTU option:
sudo nmap -sTU localhost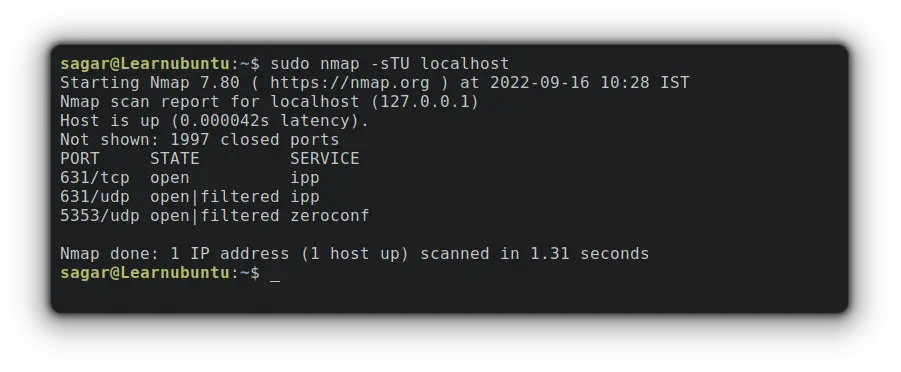
Similarly, you can also use any hostname you want. For example, let's go with google.
nmap google.com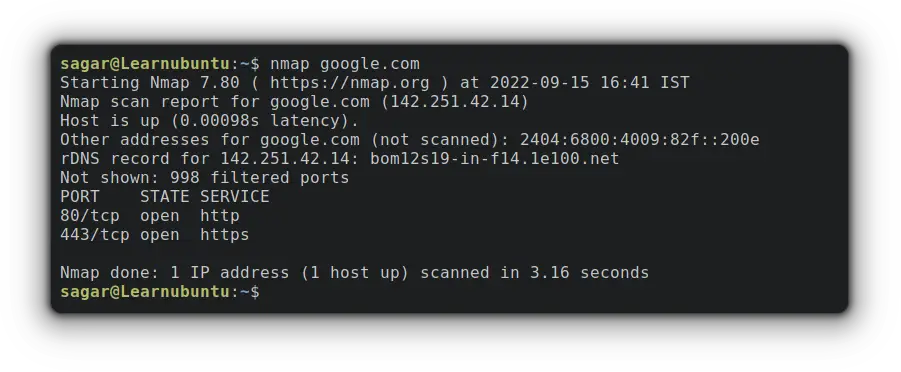
As you can clearly see, google has closed all the unnecessary ports (of course) for security reasons.
2. Using lsof Command
Linux works on the philosophy of "Everything is a File" and using the lsof (List Of) command, users can list all the open files.
As the lsof utility is bound to read data from kernel proc, you can easily trace network connections that include ports too.
But lsof command can't be used without options so you'll have to utilize certain options to get open ports.
So first let me show you the command and then we'd jump to the explanation:
sudo lsof -i -P -sTCP:LISTEN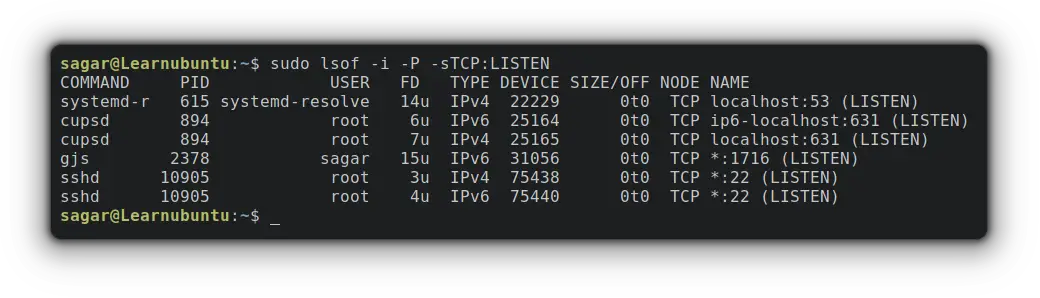
Now, let me break down the used options:
-l is used to get files that are only related to networks.
-P displays the numeric value of ports.
and -sTCP:LISTEN will fetch TCP ports in the listening (open) state.
In a similar fashion, you can also check for individual ports. So let's suppose I want to check for port no 631 so my command would be:
sudo lsof -P -i:631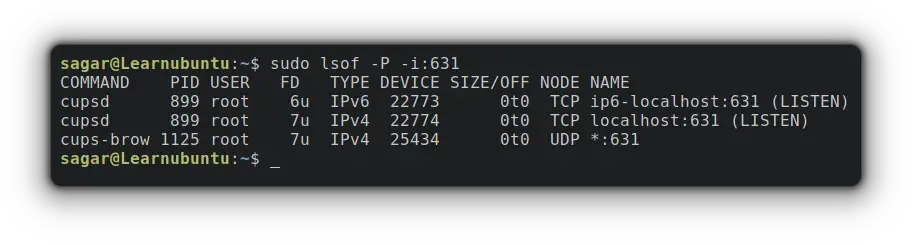
As you can clearly see the cupsd is being utilized by the root on the given port.
3. Using ss Command
Yep, this is the same command that I discussed at the beginning of this tutorial but here, I'm going to cover more possibilities.
So the ss (Socket Statistics) is a CLI utility used to get socket information. And being part of the iproute2 package, you get faster and more in-depth info compared to others.
And to list ports that are in listening state, you'd need to use the given command:
sudo ss -tulwnp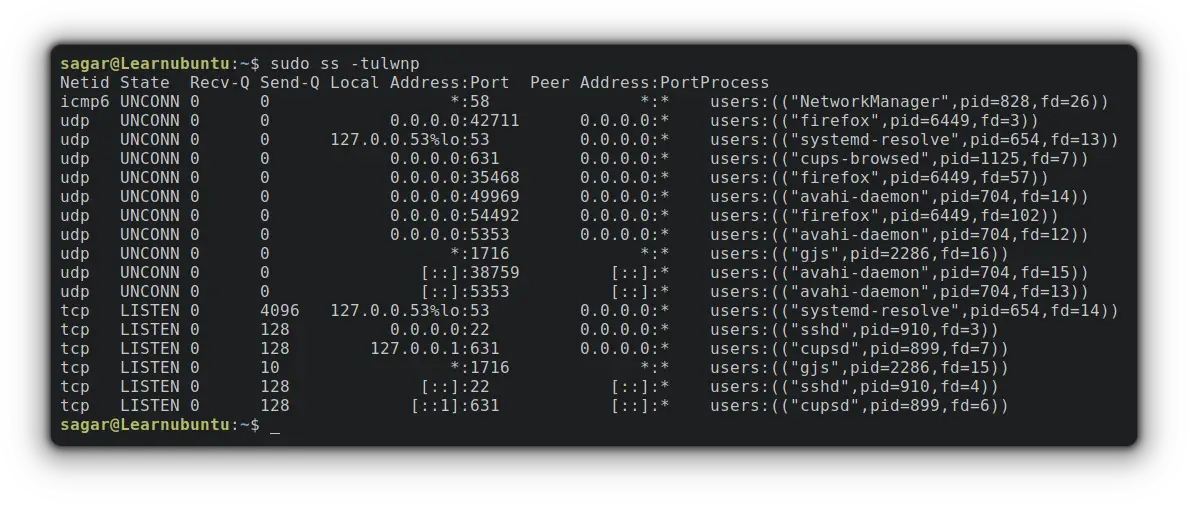
Here,
-l is used to list open (listening) ports.
-t and -u are used to get TCP and UDP ports respectively.
-n shows the exact bandwidth value.
-p shows processes using sockets.
and -w is used to get raw sockets (sockets that provide access to lower-layer protocols).
Final Words
This guide explained multiple ways to list open ports. I'd recommend you to use the ss command instead of netstat command which is deprecated and should no longer be used.
A software engineer who loves to tinker with hardware till it gets crashed. While reviving my crashed system, you can find me reading literature, manga, or watering my plants.

